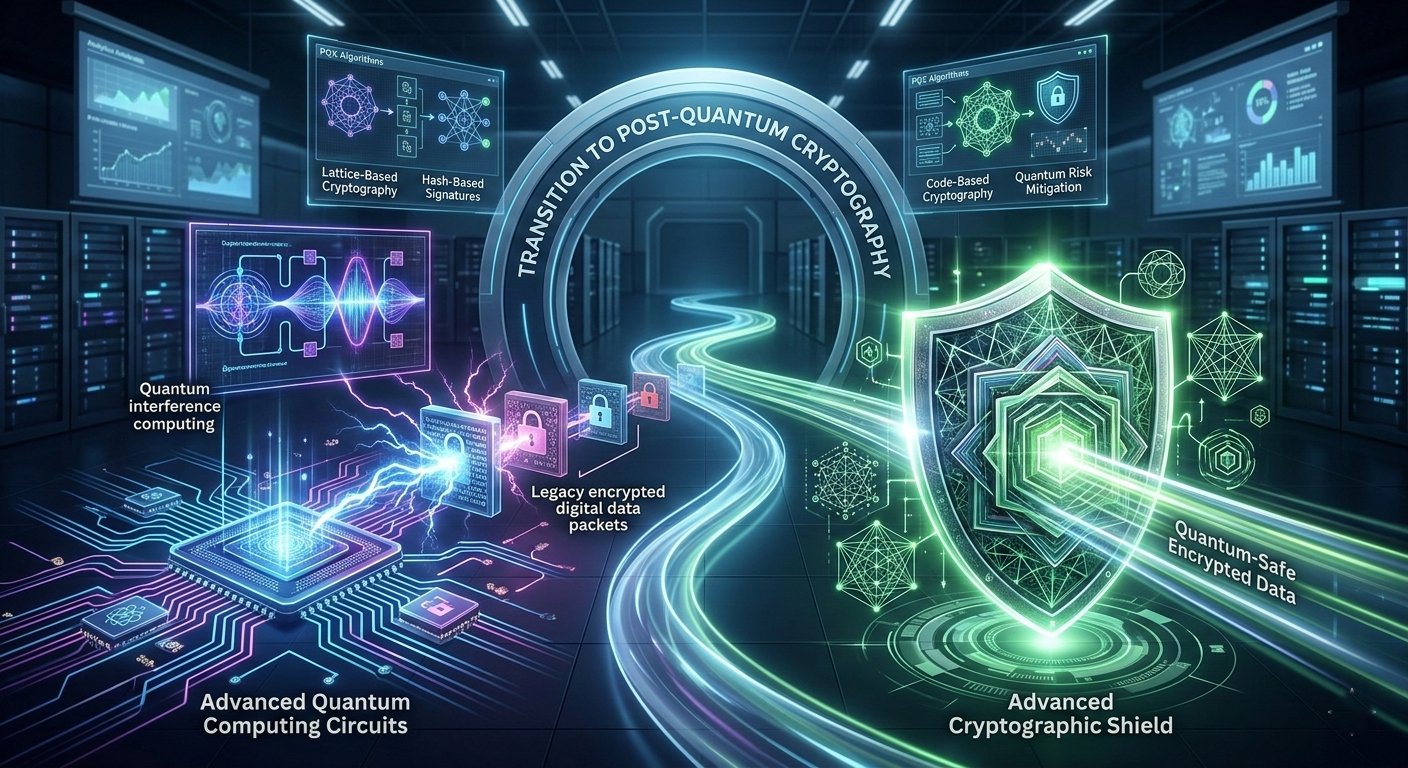
As quantum computing continues to advance, traditional encryption methods that protect sensitive digital data are facing a potential future threat. Post-Quantum Cryptography is emerging as a crucial solution for organizations that want to stay secure in the age of quantum computing. While today’s encryption standards remain effective for now, experts warn that quantum computers could eventually break many of the cryptographic systems that currently safeguard global data.
For enterprises managing sensitive information, preparing early for the shift toward post-quantum cryptography is becoming a strategic cybersecurity priority.
What Is Post-Quantum Cryptography?
Post-quantum cryptography refers to cryptographic algorithms designed to withstand attacks from both classical and quantum computers. Unlike traditional encryption systems such as RSA or ECC, which rely on mathematical problems that quantum machines could potentially solve quickly, post-quantum algorithms are built on problems believed to remain secure even in a quantum computing environment.
The goal is simple: ensure that data remains protected even when quantum computers become powerful enough to challenge current encryption standards.
Organizations like the National Institute of Standards and Technology are already working on standardizing post-quantum cryptographic algorithms to help enterprises transition smoothly to quantum-resistant security systems.
Why Traditional Encryption May Become Vulnerable
Most modern digital security systems rely on encryption methods like RSA and Elliptic Curve Cryptography. These methods protect everything from financial transactions to confidential corporate communications.
However, the development of quantum computers, particularly those using algorithms like Shor’s Algorithm, could potentially break these encryption techniques by solving complex mathematical problems significantly faster than classical computers.
If large-scale quantum computers become operational, attackers could decrypt sensitive data that was previously considered secure.
This risk has created what cybersecurity experts call “harvest now, decrypt later” attacks, where attackers collect encrypted data today with the intention of decrypting it once quantum capabilities become available.
The Growing Urgency for Enterprises
Organizations across industries are beginning to recognize the importance of transitioning to quantum-resistant security strategies. Sensitive data such as financial records, healthcare information, intellectual property, and government communications may need to remain secure for decades.
According to research from the World Economic Forum, the shift toward quantum-safe encryption is expected to become a global cybersecurity priority within the next decade.
Enterprises that delay preparation may face significant risks when quantum computing becomes commercially viable.
Key Technologies Behind Post-Quantum Cryptography
Post-quantum cryptography relies on several mathematical approaches that are believed to be resistant to quantum attacks. Some of the most promising methods include:
Lattice-Based Cryptography
This approach relies on complex lattice problems that remain extremely difficult for both classical and quantum computers to solve efficiently.
Hash-Based Cryptography
Hash-based signatures provide strong security guarantees and are already used in some specialized applications requiring high levels of trust.
Code-Based Cryptography
These systems rely on error-correcting codes and have been studied for decades as potential quantum-resistant encryption methods.
Multivariate Cryptography
This method uses systems of multivariate polynomial equations that are extremely challenging to solve computationally.
These techniques are currently being evaluated as part of the global effort to develop standardized quantum-safe encryption frameworks.
How Enterprises Can Prepare Today
Even though large-scale quantum computers are still developing, organizations should begin preparing their cybersecurity infrastructure today.
Conduct Cryptographic Assessments
Enterprises should identify where traditional encryption algorithms are currently used across their systems.
Develop Crypto-Agility
Crypto-agility allows organizations to quickly replace or upgrade encryption methods without rebuilding entire systems.
Monitor Emerging Standards
Organizations should stay updated with guidance from standards bodies such as the National Institute of Standards and Technology to ensure future compliance.
Protect Long-Term Sensitive Data
Industries that handle long-lived confidential information must prioritize quantum-resistant security strategies early.
Preparing now helps organizations avoid rushed and costly transitions in the future.
The Future of Quantum-Safe Security
The transition toward post-quantum cryptography will likely happen gradually over the next decade as quantum computing capabilities continue to evolve. Governments, financial institutions, healthcare providers, and technology companies are already exploring quantum-safe security frameworks to protect their data infrastructure.
The organizations that begin planning today will be better positioned to handle future cybersecurity challenges while maintaining trust with customers and partners.
Conclusion
Quantum computing promises remarkable breakthroughs across science and technology, but it also introduces new security challenges for the digital world. Post-quantum cryptography represents a proactive approach to protecting sensitive information against future quantum threats. By evaluating current encryption systems, adopting crypto-agile infrastructure, and preparing for emerging standards, enterprises can ensure their data remains secure even in the quantum era.
The shift to quantum-resistant security may not happen overnight, but organizations that start preparing today will gain a critical advantage in safeguarding their digital assets for the future.